Political Forensics: What Farage’s phone hacking claim tells us – and what it doesn’t
Digital forensics experts rarely find themselves in national headlines – but this week has been an exception.

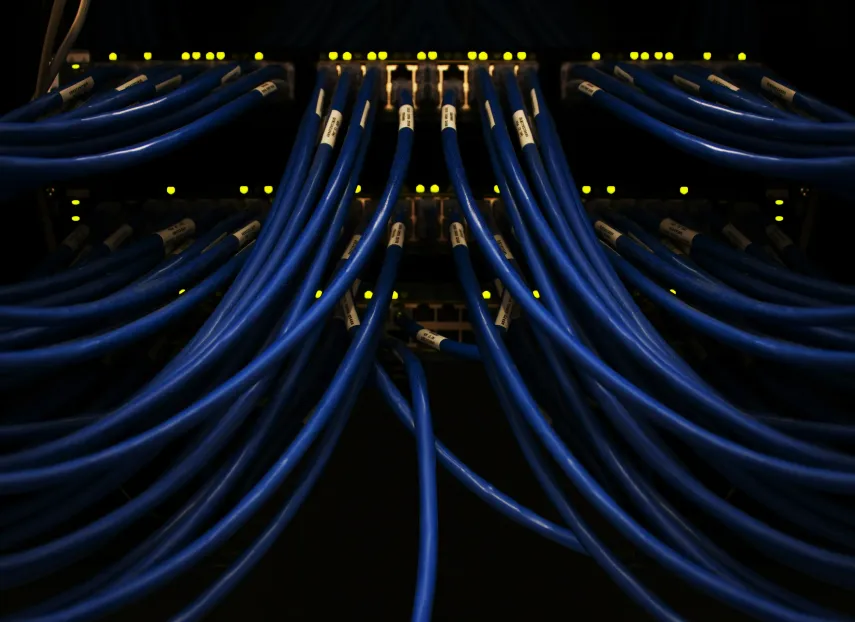
Azure Withstands Largest Cloud-Based DDoS Assault Ever
Azure stopped a record 15.7 Tbps DDoS attack from the Aisuru botnet. No downtime reported, proving the need for automated cloud defences.

Gainsight–Salesforce Apps Breach Sees Data Stolen
ShinyHunters breached Gainsight apps to access Salesforce data of 1,000 firms. Tokens revoked. Review third-party SaaS integrations now.

Company Loses US$ 11 Million After Solver Exploit Exposes Risks in DeFi Bridges
DeFi bridge Garden Finance loses $11m after a solver exploit. Experts question system autonomy as the firm offers a bounty for return of funds.
China-Linked Hackers Target Cisco Firewalls in Global Campaign
China-linked Storm-1849 targets Cisco ASA firewalls via zero-days. Attackers implant persistent malware. Immediate patching and forensic audit needed.
Major Crypto-Fraud Ring Uncovered by Europol
Europol and Eurojust dismantled a €600m crypto-fraud ring. The October 2025 operation led to 9 arrests and seizure of criminal assets across Europe.
Hackers Using Hidden Virtual Machines for Stealth Malware
Russian group Curly COMrades hides malware in Alpine Linux VMs on compromised hosts. This stealth technique evades standard EDR tools.

Flaws in Microsoft Teams Open Door for Attackers
New MS Teams flaws allow attackers to rewrite chats and spoof IDs. Patched Oct 2025—ensure all clients are updated to prevent social engineering.

Why Hackers Love Christmas as much as the rest of Us
The Christmas trading period brings huge opportunity, but it also brings heightened cyber risk.
Changing Your MDR Provider – Your Essential Checklist
This checklist is designed to make changing your managed detection and response (MDR) provider a smooth, secure, and efficient process: turning a potential disruption into a confident, well-managed upgrade.